Getting Your CRM Security Aligned
17 Aug 2023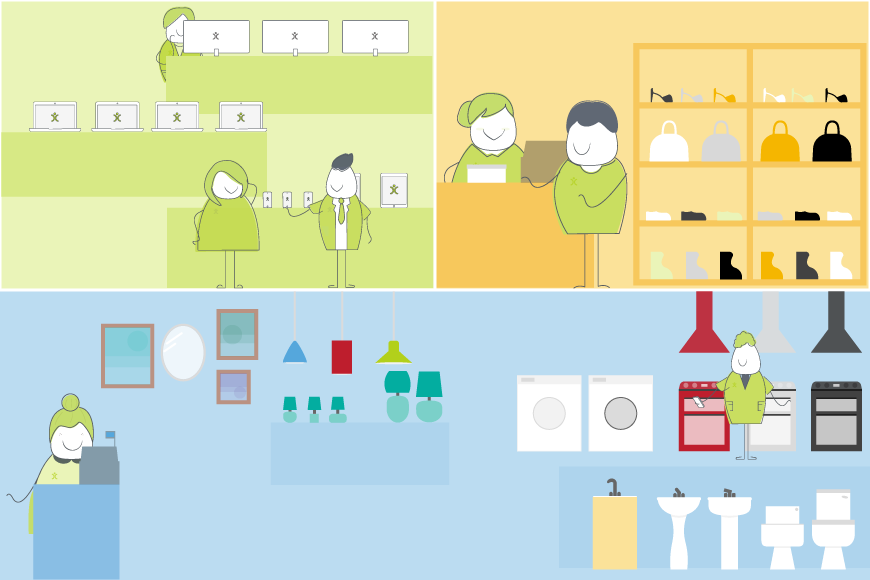
(Republished from an earlier article)
CRM Security is a vast topic but it is also one that needs to be addressed. It may be tempting to bury your head in the sand and hope for the best, but you do need to give it some thought. This might seem quite daunting so in today’s blog post we are going to break it down into manageable chunks.
Security online works both ways too. If you leave something too easy to access, then you are inviting nefarious activity. For obvious reasons you have a password for your email account, and you don’t share that with anyone, least of all strangers. We’ve read countless articles outlining the importance of secure passwords too. But if you come up with security solutions that are overly complicated, it becomes a hindrance.
CRM Security is about finding a balance that lets your team go about their day-to-day safe in the knowledge that appropriate security levels are in place. For this post, I’d like to break this into three definite areas: People, Data, and System.
The People aspect should be self-explanatory but more on that shortly. Data is the information you enter, and the System is the architecture that contains the information in a logical fashion.
Let’s Go Shopping
To illustrate the story, I’m going to reinvent your software as a department store and consider the CRM security that needs implementation in that environment.
My department store has those same three attributes that your CRM system has:
- The People are your stakeholder groups: management, members of staff and customers.
- The data is all the information you store. Customer details, product inventory, supplier details and that kind of thing.
- The System is your physical buildings – ranging from the locks on the doors, the shop itself, the storage rooms and offices.
We’re now going to look at how my different stakeholder groups interact with the department store. We can then see how that be compared to the CRM security measures and permissions you need to think about.
Your Customers
When the shop is open, people can come in and look around. They can see the goods and the prices. Some higher-value goods are probably not on direct display but require a member of staff to unlock a cabinet to show the item. You could consider this person to be someone with low-security privileges. Physically they can come and go in your shop during your opening hours, but they cannot go beyond that customer-facing zone. They can also visit the website and online store and log questions via email or social media.
If we apply that scenario to a CRM, the CRM security measures are pretty simple. The general public doesn’t possess the information required to log into your system. They can only see the data that you have marked as being customer-facing – for example through a portal. Customers can also log into that portal to view their sales history, and to log tickets with your customer support team. Quite similar to what some shops offer with their loyalty programmes. Data visibility is restricted to their own information, they cannot see information relating to other clients. Regarding the system architecture, they have very limited access to your system. Most of the modules are off-limits, and the functionality available is very restricted.

What do you get with OpenCRM?
Unrivalled customer support? 2TB of storage per account? Data held in EU? It's the sort of stuff we think you should be able to take for granted, but which you won't necessarily get from our competitors.
find out moreStandard Users
Let’s say your front-of-house staff all have an ID that lets them into the building. This is like the username and password your team uses to get to their account in the CRM. As well as walking around the customer-facing areas, your staff can also go behind the counters, into the warehouse and other places off-limits to clients. They can log into computers to process sales, check stock alerts, give discounts, create new loyal customers and that kind of thing.
Let’s look at this in CRM terms. These members of staff can log into the system. If you have heightened security awareness, you might want to implement Multi-Factor Authentication on top of the usual username and password to enable access.
Once logged in, they can view customer details, to input or update records. They can log sales on the system, and you might even set their accounts up so they can apply discounts, within reason. But they cannot edit your product data itself which could mess with your ordering processes, and they cannot see or alter your buy prices either.
In terms of system architecture, depending on their log-in, they will have access to different areas of the system. Sales staff will not need to see the Helpdesk area that the Support department use. None of them can see Personnel data, apart from perhaps their own record, so they can view their holiday allowance.
Line Managers
Your management team will need to know everything happening in the shop regarding the sales team – that’s where line managers come into play. This is a vital role as it involves explaining to the sales team how they put the corporate vision into practise. As per that stakeholder group, they can access the shop front, warehouse, canteen, staff parking and so on. They tend to spend their time in the offices upstairs, rather than in the customer-facing areas.
Managers need access to different areas of the system than your sales staff. If we flip this to OpenCRM speak – your managers can access and create activities for all the members of their team (working out staffing rotas for example). For this, they need a comprehensive overview of the personnel data.
In terms of data and overall module accessibility, the managers have far more access than the sales team. A different role in the business means physical admittance to more places and also increased data access.
Inventory Managers and CRM Security
You have a team that looks after what’s on the shelves. The inventory managers will decide what to buy, input product and price details from suppliers, and set sell prices.
These are your data admins. They will be permanently updating product lists, altering buy prices, inputting supplier details and that kind of thing. They will also update the system itself, carrying out actions such as modifying picklists and adding custom fields. This will require a profile with quite a different set-up from the previous stakeholder groups we have considered. They are less concerned with customer or personnel data, so access to those modules can be restricted.
Senior Management
You need to have a person or team with an overview of everything that is going on. Reviewing sales and performances, keeping tabs on finance, and basically overseeing the business plan. They also have the keys to the boardroom and the company accounts. Information-wise, they have access to sensitive information that is for management eyes only.
In your CRM security considerations, these are the system/ super admins. They have access to all data and all configuration. If anything needs altering, they can be on there right away. If a staff member needs to be locked out of the system or added in, they can do that. There may be sensitive information that no one else should see. Once again, using permissions at module and field level means you can streamline the system to ensure the right people have access to the right information.
A few words on Social Engineering (Look Before You Leap)
As well as addressing security internal security questions, you need to look beyond your own four walls and consider the wider world. Social engineering fraud is becoming more prevalent in the business world. Even if you think your business is relatively niche or not worthy of targeting, you may be surprised. I mean, who thought that scams specifically against football clubs would be a thing?
With the rise of video and screen sharing over the past couple of years, it has become incredibly easy for someone to engage in a conversation, and share a link in the comments that someone else might click on.
Protect Yourself
It is worth being prepared for such scenarios. Here at OpenCRM, we use a variety of methods to be certain that the person we are speaking to, really is who they say they are. Sometimes this can cause short-term irritation for the end-user, but effectively when people understand that it is their entire business database that might be at risk, then they can see why we err on the side of caution. As Forbes says, “validate everything and everyone, everywhere”
Your Business and CRM Organisational Structure
As you can see, there are parallels in how the hierarchy in your organisation needs to be reflected in your CRM set-up. There is quite a lot to think about when setting this up. Your CRM security model needs to offer the appropriate level of safety without compromising on usability. As you are likely to have a remote workforce also using and interacting with the system, it is important to get your permissions model in place when setting up your CRM.
My role is to build our Customer Success team and I work with our clients and prospects helping them get the most from their subscription – it is a fun challenging role as no two days are the same. When not in the office I’ll be either making a noise on my guitar or getting my trainers on for a run out in the Yorkshire Dales, North York Moors or the Lake District.